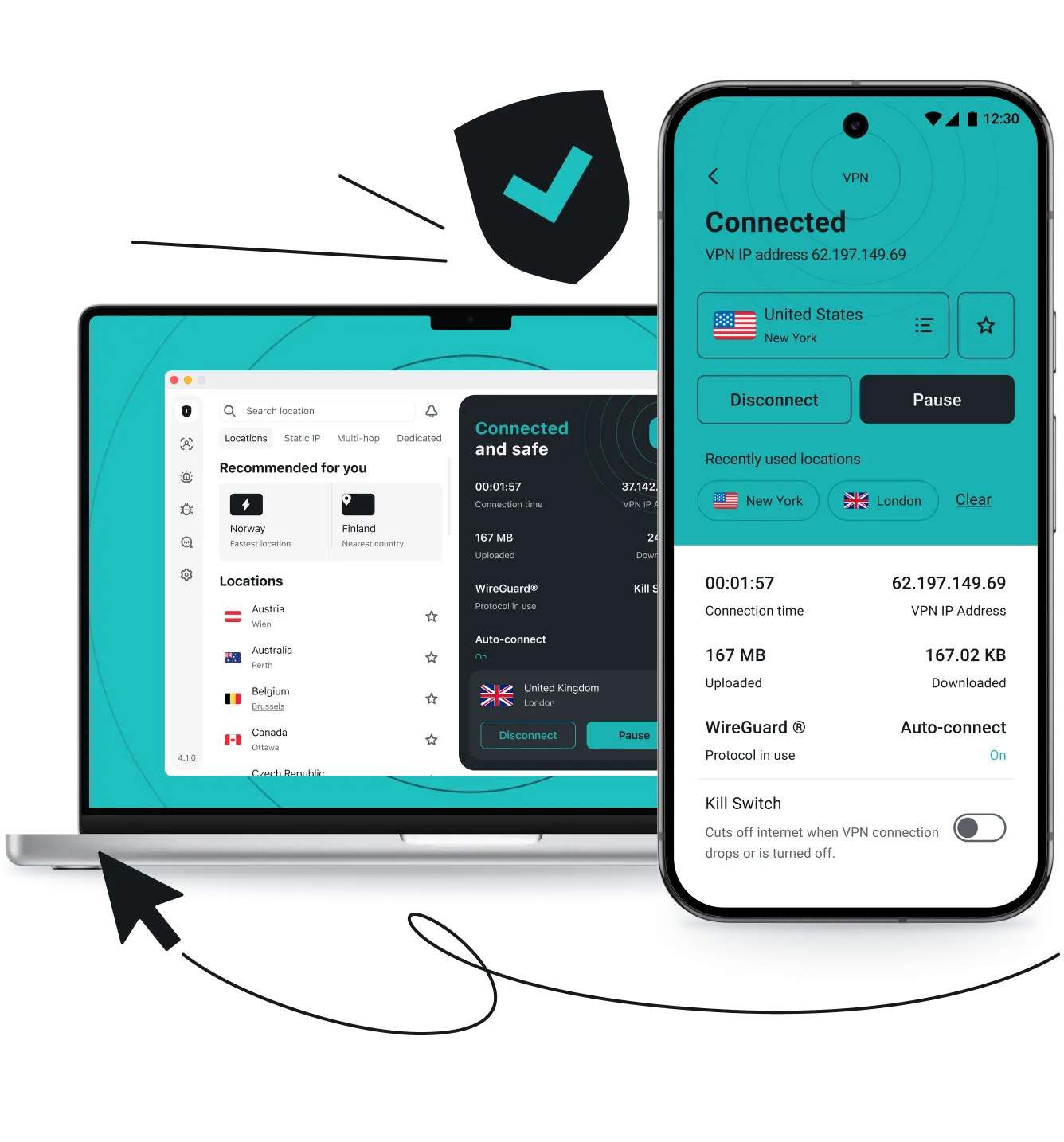
A VPN, or virtual private network, is a service that routes your internet traffic through a secure, remote server. It encrypts your internet traffic and masks your IP (Internet Protocol) address.
This process secures your connection to the internet and protects your privacy while browsing online. It also hides your online activities from third parties trying to collect your data or intercept your connection.