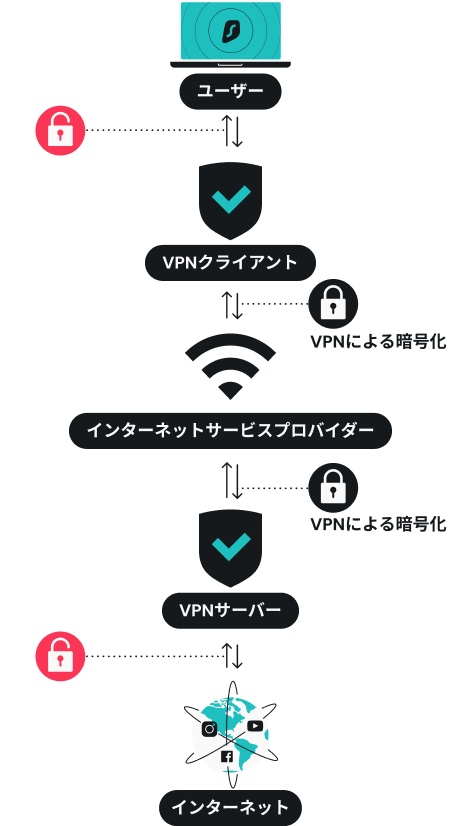
VPNは、インターネット通信を専用のVPNサーバーに経由させることで、データを暗号化し、IPアドレスを隠します。通常、通信はユーザーのデバイスから直接ウェブサイトへ送信されますが、VPNを利用するとその経路が変わり、安全なトンネルを通じて通信が行われます。
この仕組みにより、通信内容は第三者に読み取られにくくなり、ユーザーのIPアドレスも秘匿されます。結果として、あたかもVPNサーバーが設置されている地域からアクセスしているように見えるため、プライバシー保護やセキュリティ向上につながります。
- 安全な接続を構築する
VPNに接続すると、デバイスとインターネットの間に「仮想トンネル」と呼ばれる安全な通信経路が構築されます。このトンネルは外部からの干渉を受けにくく、全ての通信データはこの中を通って送受信されます。特に公共Wi-Fiのようなセキュリティが不十分な環境でも、通信の盗聴リスクを大きく低減できます。
- IP アドレスを変更する
VPNを経由した通信では、ユーザーの実際のIPアドレスは外部に公開されず、代わりにVPNサーバーのIPアドレスが表示されます。これにより、アクセス先のウェブサイトやサービスからユーザーの位置情報や個人の特定がされにくくなります。また、サーバーの設置場所を選択することで、異なる地域からアクセスしているように見せることも可能です。
- データを暗号化する
VPNは通信データを強力な暗号技術で保護します。暗号化されたデータは第三者にとって意味のない文字列として扱われるため、万が一通信が傍受された場合でも内容を読み取られることはありません。ログイン情報やクレジットカード情報などの重要なデータも安全にやり取りできるため、安心してインターネットを利用できます。