
Phishing – the type of internet scam that relies on tricking people into believing that they’re working with a genuine service – grew ever more in the face of the pandemic. While phishing sites remain one of the most visible aspects of this digital scam, emails have not stopped posing a threat. So how do you spot a phishing email?
Recognize a phishing email by:
- Checking the sender’s domain
- Looking at how you’re addressed and what name is used
- Spotting grammar mistakes
- Looking out for information requests
- Inspecting link addresses without opening them
- Identifying distrusftful attachments
- Getting suspicious of urgency and too-good-to-be-true offers
What is phishing?
Phishing is a type of scam or hack that exploits the human link in the digital security chain. Phishing can take many forms, from fake websites that are made to look genuine to emails that pretend to come from real companies to even text message scams. The goal is always the same: to make you give the hackers your data.
What is a phishing email?
A phishing email is a scam that relies on emails. A hacker crafts an email that looks like it’s coming from a genuine source, like the support department at Google or Amazon or someone from work (spear-phishing). However, unlike real support emails, they request sensitive data the actual company would never ask for: your login and password or your security questions.
Sometimes, such scam emails work in tandem with fake websites. Instead of asking for your data, they give you a phishing link to a website that looks like the real thing. When you enter your login data, the fake website might even direct you to your actual account, but the hacker will already have stolen your information.
Another possibility is infecting email recipients via email attachments. An enormous Amazon scam sent empty emails with attached Word documents. To open the document, the users were asked to enable macros – and those macros then installed malware on their devices.
How to identify a phishing email
You can use a tool like Surfshark’s email scam checker to scan messages in your Gmail inbox for possible phishing attacks. Alternatively, you can take the following steps to check emails yourself for the tell-tale signs of a scam.
- Check the domain: legitimate companies have their own domains. For example, Surfshark will never write to you from “surfshark@gmail.com.” Of course, scammers might try to trick you by using domains that are close-enough, like “support@srfshark.com” or so.
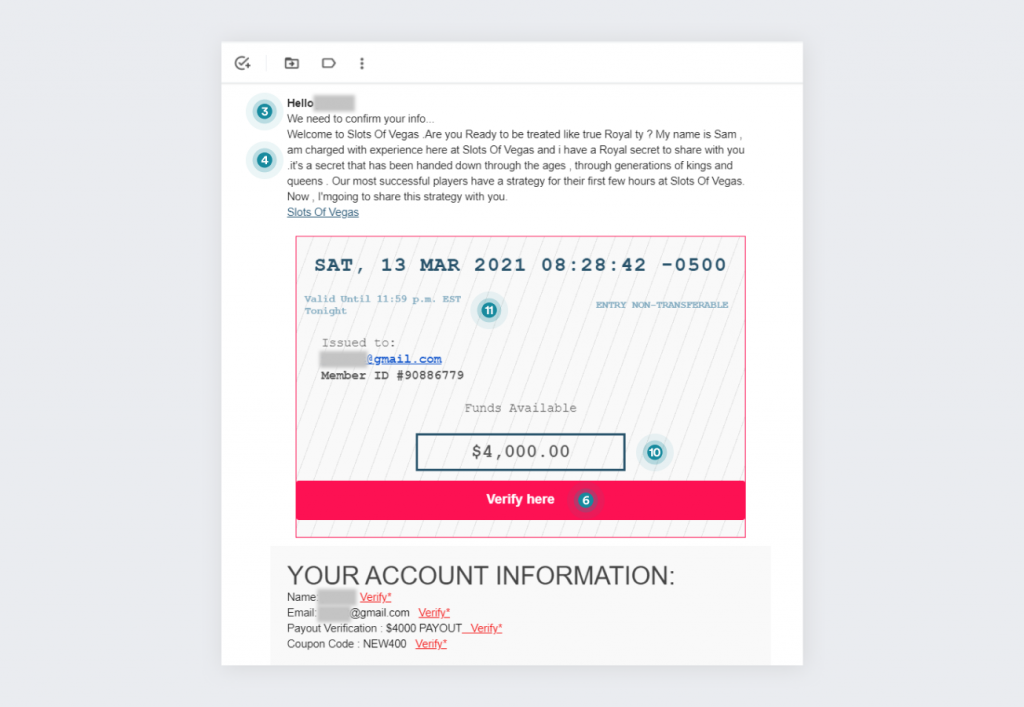
- Look at how you’re addressed: if a company representative is writing to you, they have the name you registered with on file and will use it in the form. “Hi Dear” and “Dear Customer” are the sorts of vague salutations that signify scam emails.
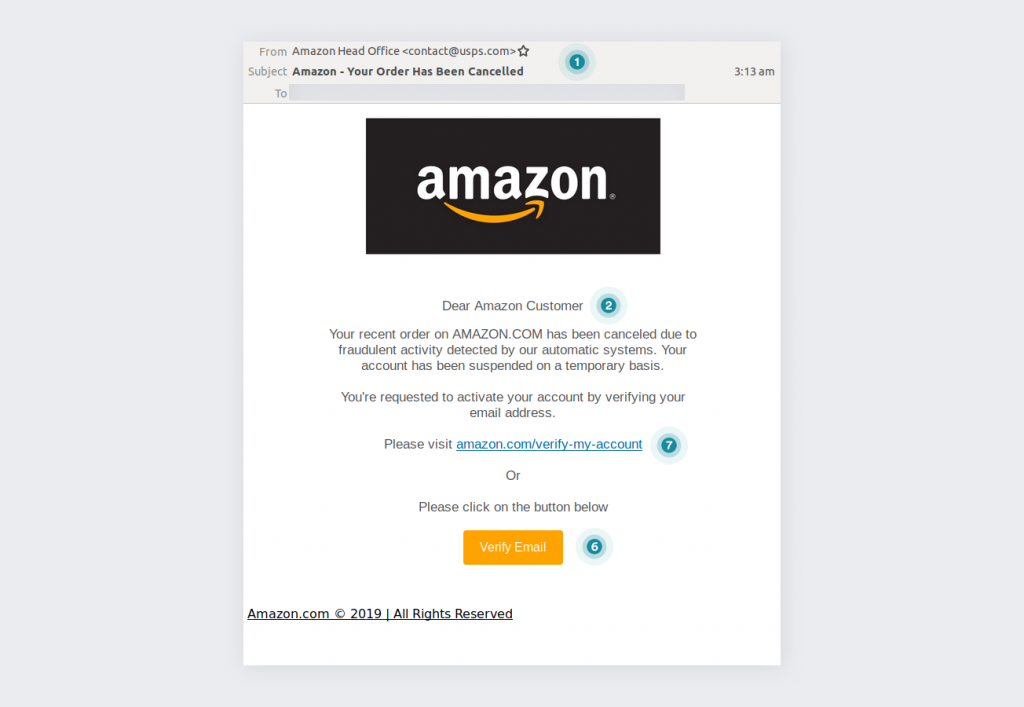
Source: MailGuard
- Make sure it’s really your name in the email: hackers may use the part of your address preceding the @ to make the greeting look real. You’ll easily notice that this is a scam if the email address is something like “FirePowerDog@gmail.com” meaning that the email will begin with “Hello, FirePowerDog.” If you use email masking, the name will be even weirder. But it may trick inattentive or less digitally literate people who use their names and surnames as part of the address.
- Be on the lookout for grammar mistakes: the bigger the company, the more money and time they’ll have dedicated to ensuring that all their emails are squeaky clean and error-free. Scammers don’t have such concerns, primarily relying on the fact that most people only do a surface-level scan of an email.
- Beware of information requests: legitimate companies do not ask you for your login information, security questions, or other such information. None of these are needed for the company to manipulate your account – they have the backend tools for that.
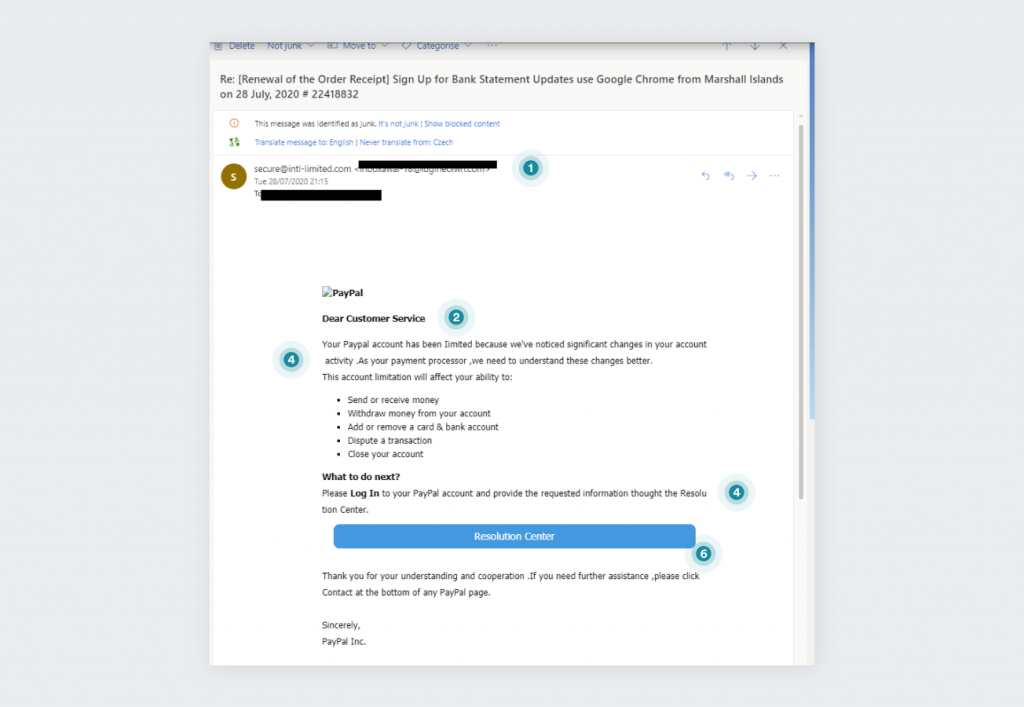
Source: Malwarebytes
- Watch out for links: phishing emails will push you to click the provided links. It is likely to lead to a cloned website where any information you enter will be stolen. It’s always better to go to the website like you normally would via the browser and then carry out the operations the email wants you to do (if you believe it to be legitimate, that is).
- Inspect the link addresses: you can check the links by just keeping your cursor over them. If every link in the email leads to the same URL, it’s a phishing email. Also, while the hackers may try to trick you by adding words associated with the legitimate business somewhere in the address, they can only do it by adding it to their original URL. So instead of “netflix.com,” you’d get “netflix.cargo.com” or “netflix.com.cargo.com.” Also, if any of the links lead to a link shortening service like bit.ly, it’s proof that a hacker is trying to phish you. Link shortening services are used to bypass filters and firewalls.
- Spot the attachments: another big warning sign is an unsolicited attachment. If you did not expect to get an email with a file attachment, one that contains it is immediately suspect. If the email contains nothing but a file, it’s obviously a phishing email.
- Be suspicious of once-in-a-lifetime offers: just like we learned that banners proclaiming us to be the 1,000,000th visitor are lying, we should also be aware that emails promising some unforeseen financial benefit (we recommend being mindful of lifetime VPN promises), unexpected winnings, or random romantic offers are trying to trick us.
- Recognize suspicious urgency: the urgency itself might be an indication that this is a phishing attack. Of course, big companies also want you to act fast on whatever they want you to do, but they use language that is more careful.
What to do if you opened a phishing email
Opening a phishing email by itself shouldn’t be dangerous – but clicking any links or downloading attachments is! Either way, it’s always smart to report a phishing email to make the internet safer for all of us. More about how to report emails in a bit, let’s get to the more urgent stuff now.
What to do if you clicked a link in a phishing email
Clicking on phishing links is one of the most dangerous things you can do when dealing with these emails. Here are the procedures to follow if you click on any of them:
- Disconnect the device from the internet.
- Run an antivirus scan.
- If you entered any bank details, notify your bank (or credit card provider) of what happened.
- If you entered any login data, go to the website directly (and not via any links), and change the password and other login information (like password reset questions).
- Check that your personal data on the affected account – such as password recovery means, phone number, postal address – are still correct.
- Remove any authorized devices you don’t know/own, as hackers may have authorized their own.
- Activate two-factor authentication where possible
- Cancel any orders that were made by hackers.
- Remove credit cards that were stored on compromised accounts to deny the hackers any pertinent data.
- Warn your contacts and relatives about what happened to you – this can help them avoid falling for similar scams.
What to do if you opened an attachment in a phishing email
When it comes to phishing emails, attachments are rarer than links. However, they are no less dangerous. Here’s what you can do if you opened an attachment in a phishing email:
- Disconnect from the internet.
- Run an antivirus scan.
- Do that after a few days as well.
- Consider contacting a specialist to check if you’ve been hacked.
In both of these cases, having backups of the data on your device beforehand would help minimize the impact.
Can a VPN protect you from phishing emails?

A VPN can protect you from phishing attacks if the developer has chosen to add that functionality. As phishing links and websites are discovered, those addresses can be indexed – and blocked. So having a VPN on can block some of the malicious links that come in phishing emails. However, it’s still best to learn how to recognize phishing emails and avoid them.
Use an integrated email alias
You can protect your email from phishing using a VPN that offers an email alias, like Surfshark’s Alternative ID. It creates new credentials and an alternative email address for you to use online. It’s not a cure-all, but it prevents spam that could be phishing attacks from coming to your real email.
Using Alternative ID reduces the chances of your regular credentials and email address being leaked or sold to third parties (which usually results in phishing scams).
How to report phishing emails
Reporting phishing emails makes the digital realm safer for all of us. Note on phishing reports: keep the email headers intact, and don’t expect the services to respond to you personally. Here are several ways to do it:
Report phishing emails in the US:
- Forward the email to reportphishing@apwg.org.
*If you received a phishing text message, forward it to SPAM (7726)
- Report the phishing attempt to the FTC.
Report phishing emails in the UK:
Forward the phishing email to report@phishing.gov.uk.
Report phishing emails on Gmail:
- Open the suspicious email in Gmail.
- Click More (three dots) next to the Reply arrow.
- Click Report phishing.
Report phishing emails on Outlook.com
- Select the suspicious message.
- On the reading pane, click Junk, then Phishing, then Report.
Report phishing emails to Amazon:
- Start a new email and attach the suspected phishing email to it.
- Send it to stop-spoofing@amazon.com.
- If you can’t attach the email, just forward it to stop-spoofing@amazon.com.
Report phishing emails to Apple:
- In the OS X Mail menu, select the message and choose Forward As Attachment from the menu.
- Send it to reportphishing@apple.com.
- If you’re not using Mail, forward the message (preferably as an attachment) to reportphishing@apple.com.
Report phishing emails to PayPal:
Forward the unaltered message to spoof@paypal.com
Note: Make sure you don’t alter the header or forward the message as an attachment.
Report phishing emails to Netflix:
- Forward the email to phishing@netflix.com.
- If the email is rejected, Netflix has already been notified of that specific phishing email before.
Report phishing emails to Coinbase:
If you think you’ve received a Coinbase scam email, forward it to security@coinbase.com.
Recognize the threat of phishing emails
You should have a good idea of how to recognize a phishing email once you receive one. And now you know how to defend yourself:
- Regularly back up your data
- Have updated antivirus software
- Don’t open suspicious links or attachments
So our last bit of advice is this: get Surfshark VPN – the benefits extend beyond security!




