One of the most important — and often misunderstood — aspects of VPN (Virtual Private Network) performance is the VPN protocol itself. VPN protocols dictate how your data moves across the internet, influencing your connection’s speed, stability, and usability.
In this article, we’ll clearly explain common VPN protocols, correct misconceptions, and help you determine which protocol is truly best for your everyday needs.
What is a VPN protocol?
A VPN protocol is essentially a collection of rules and standards that allows your device to securely access or connect to a remote private network over the internet. Each VPN protocol defines exactly how your data is encrypted, authenticated, and transmitted between your device (client) and the VPN server, ensuring a private and secure connection. Think of it as the underlying technology that allows a VPN to function.
What we refer to as a VPN protocol is actually a combination of multiple standardized protocols working together. Each VPN solution (like Dausos, OpenVPN, IKEv2/IPsec, or WireGuard) is composed of specific sub-protocols responsible for tasks like authentication, key exchange, encryption, integrity checking, and data transport.
When choosing a VPN protocol, practical considerations include:
- Security: how data is encrypted and protected;
- Speed: the impact of encryption and protocol overhead on your connection’s performance.
- Stability: maintaining consistent connection quality, especially during network changes.
- Compatibility: support and ease of use across different devices.
Importantly, modern VPN protocols offer similar high-level security standards, so differences in security typically come down to correct configuration rather than the protocol itself.
Common VPN protocols
Today, WireGuard, OpenVPN, and IKEv2/IPsec dominate VPN technology. All three are open-source, allowing public audits and continuous security improvements. While they provide comparably strong security, each differs significantly in performance, complexity, and ideal use cases:
WireGuard
WireGuard is a modern, streamlined VPN protocol designed specifically for speed, security, and simplicity. It’s now considered an industry standard.
| Pros: |
|---|
| Built-in support on most modern devices, especially mobile; |
| Excellent stability and quick reconnection, especially when roaming on mobile networks; |
| Strong, reliable security based on IPsec encryption. |
OpenVPN
OpenVPN is a well-established VPN protocol recognized for its extensive configurability and reliable performance. It supports both UDP and TCP modes — UDP being slightly faster, and TCP providing more reliable data delivery (retransmission of lost packets).
| Pros: | Cons: |
|---|---|
| Highly customizable, compatible with a wide range of platforms and devices; | Generally slower due to higher overhead; |
| Rich ecosystem of plugins and configuration options, allowing advanced functionality, such as traffic obfuscation (masking VPN connections as normal HTTPS traffic); | Requires installing additional client software, adding complexity to the initial setup. |
| Proven reliability and widespread industry support. |
IKEv2/IPsec
Internet Key Exchange version 2 (IKEv2) uses IPsec (Internet Protocol Security) for encryption and is a good choice for mobile devices because it is able to swiftly change networks (e.g., between Wi-Fi and mobile). However, it’s important to note that today, WireGuard performs even better since it doesn’t lose connection when changing networks in the first place.
| Pros: | Cons: |
|---|---|
| Built-in support on most modern devices, especially mobile; | Less customizable compared to OpenVPN; |
| Excellent stability and quick reconnection, especially when roaming on mobile networks; | Can be blocked on certain restrictive networks if not properly configured. |
| Strong, reliable security based on IPsec encryption. |
Legacy protocols (not recommended)
PPTP, L2TP/IPsec, and SSTP are outdated and no longer secure VPN protocols, considered inefficient for general use. While you might occasionally encounter them, modern users and companies should avoid them.
- PPTP: critically insecure and considered obsolete;
- L2TP/IPsec: offers no practical advantage over newer protocols and has compatibility issues;
- SSTP: limited primarily to older Windows systems; outdated and rarely supported today.
Surfshark’s custom Dausos VPN protocol
In addition to the three modern protocols, another option worth knowing about is Surfshark’s proprietary Dausos protocol.
Dausos is built for consumer use, combining high speeds with a secure-by-default design. With Dausos, each user gets their own private data tunnel to minimize latency. Post-quantum cryptography and AEGIS-256X2 encryption protect from current and future threats, meaning Dausos provides a powerful mix of speed, privacy, and security.
Dausos is currently available to Surfshark users on macOS from the Mac App Store, not the .dmg installer from the Surfshark website. Availability on other platforms is coming soon.
Pros:
- Faster speeds as a result of removing data-sharing bottlenecks;
- Strong privacy thanks to dedicated, private data tunnels;
- Resilient, future-ready security based on AEGIS-256X2 encryption.
Choosing the best VPN protocol for you
While all modern VPN protocols (WireGuard, OpenVPN, IKEv2/IPsec, and Dausos) meet high standards for security and reliability, they don’t have the same capabilities.
With its exceptional speeds, simplicity, and strong encryption, Dausos is the best overall choice on Surfshark, outperforming other protocols for macOS users.
However, if Dausos isn’t available, alternative options make sense in different specific scenarios:
When to consider WireGuard
Choose WireGuard for:
- Faster speeds: WireGuard offers high-speed connections, making it a strong choice for streaming, gaming, downloads, or general browsing;
- Simplicity and stability: its minimalist architecture ensures reliability and easy setup;
- Efficient mobile use: WireGuard smoothly manages network changes (roaming between cell towers, Wi-Fi networks) without interrupting your connection;
- Strong security: uses modern cryptographic standards and is continuously reviewed for vulnerabilities.
WireGuard is the best option for virtually all typical use cases.
When to consider OpenVPN
Consider OpenVPN (especially in TCP mode with obfuscation plugins) primarily if you face specific, challenging network restrictions:
- Bypassing censorship: some networks impose strict internet access restrictions, limiting legitimate content or blocking secure communications. Using OpenVPN’s obfuscation plugins on TCP port 443 can effectively disguise traffic as regular HTTPS, helping legitimate users — such as journalists, researchers, or remote workers — securely access the internet and essential resources in restrictive environments;
- Advanced customization needs: if your scenario requires unusual authentication methods, advanced security setups, or integration with other security tools, OpenVPN’s mature plugin ecosystem offers extensive flexibility.
OpenVPN’s tradeoff: slower speeds and a slightly more complex setup compared to WireGuard.
When to consider IKEv2/IPsec
Consider IKEv2/IPsec primarily if your priority is built-in, native support without additional software installation:
- Built-in platform support: IKEv2 is integrated into most major operating systems (especially mobile platforms like iOS or Android). Ideal if you prefer a native, straightforward setup without installing additional applications.
- Reliable mobile reconnection: Performs well when roaming across mobile networks or frequently changing network access points.
IKEv2/IPsec’s tradeoff: setting up the client beyond basic options is hard. Advanced settings are complicated, and users often need extra software to make everything work right.
Protocols to avoid
PPTP, L2TP/IPsec, and SSTP are older legacy protocols that are now obsolete, insecure, and generally no longer recommended. Modern users and businesses should not consider these options.
Common VPN use cases
VPNs help people do many things, from keeping personal information private to letting workers connect securely from anywhere. Modern VPN protocols like Dausos, WireGuard, OpenVPN, and IKEv2/IPsec can do different things, and the choice isn’t usually limited by the use case. Which tool you pick depends more on how fast it works, what devices it supports, and how easy it is to set up.
1. Remote Access VPN
A remote access VPN securely connects individual users (e.g., remote workers, business travelers, freelancers) to a company’s private network from any location. Employees working remotely use client software on their devices to securely access internal company resources like shared drives, databases, or applications, just as if they were physically connected to the organization’s local network.
In practice, the VPN client creates an encrypted tunnel between the user’s device and the company’s VPN server. All traffic sent over this connection remains private, secure, and protected against unauthorized access.
2. Site-to-site VPN (corporate VPN)
A site-to-site VPN securely links entire networks rather than individual users. Commonly deployed by organizations with multiple office locations or data centers, this VPN type establishes secure, encrypted connections between entire networks, allowing seamless, secure resource sharing across geographic locations.
In practice, site-to-site VPNs establish secure tunnels at the network level, usually between dedicated VPN gateways or routers at each location. Users on either network access shared resources without individually initiating VPN connections, as the VPN link remains persistently active.
3. Consumer VPN (commercial VPN services)
Consumer VPNs are commercial VPN services offered to individuals for purposes of enhancing personal online privacy, security, and freedom on the internet. Users typically subscribe to VPN providers that offer multiple public servers around the world, allowing users to browse anonymously, protect their browsing activity from ISPs or third parties, and access home content when travelling abroad.
In practice, a user’s device connects to the VPN provider’s servers, encrypting internet traffic and hiding the user’s original IP address. This protects users from various threats, including data monitoring, ISP throttling, and unauthorized surveillance.
4. Mobile VPN (VPN for roaming users)
The term mobile VPN doesn’t refer to a separate VPN technology but rather describes configurations optimized specifically for users who move frequently between networks, such as smartphones or tablets switching between mobile towers or Wi-Fi hotspots. Such VPN setups ensure uninterrupted and continuous connections, eliminating downtime or manual reconnections.
In practice, these VPNs leverage protocols (like WireGuard or IKEv2/IPsec) that handle network changes efficiently, maintaining a stable, persistent session even when the underlying network connection changes due to roaming or intermittent connectivity.
5. Browser-based proxy extensions
While commonly marketed as browser VPNs, these browser extensions are technically proxy services, not true VPNs. They encrypt only your browser’s web traffic — not the entire device — and route this traffic through remote servers, typically for basic privacy or to bypass simple content restrictions.
In practice, the extension encrypts web traffic directly within the browser. However, other apps or system-wide communications remain unprotected, limiting security benefits to basic browsing privacy or temporary access to regionally restricted web content.
Important note: Browser-based solutions do not offer comprehensive device-level protection and should not replace dedicated VPN software when strong privacy or security is needed.
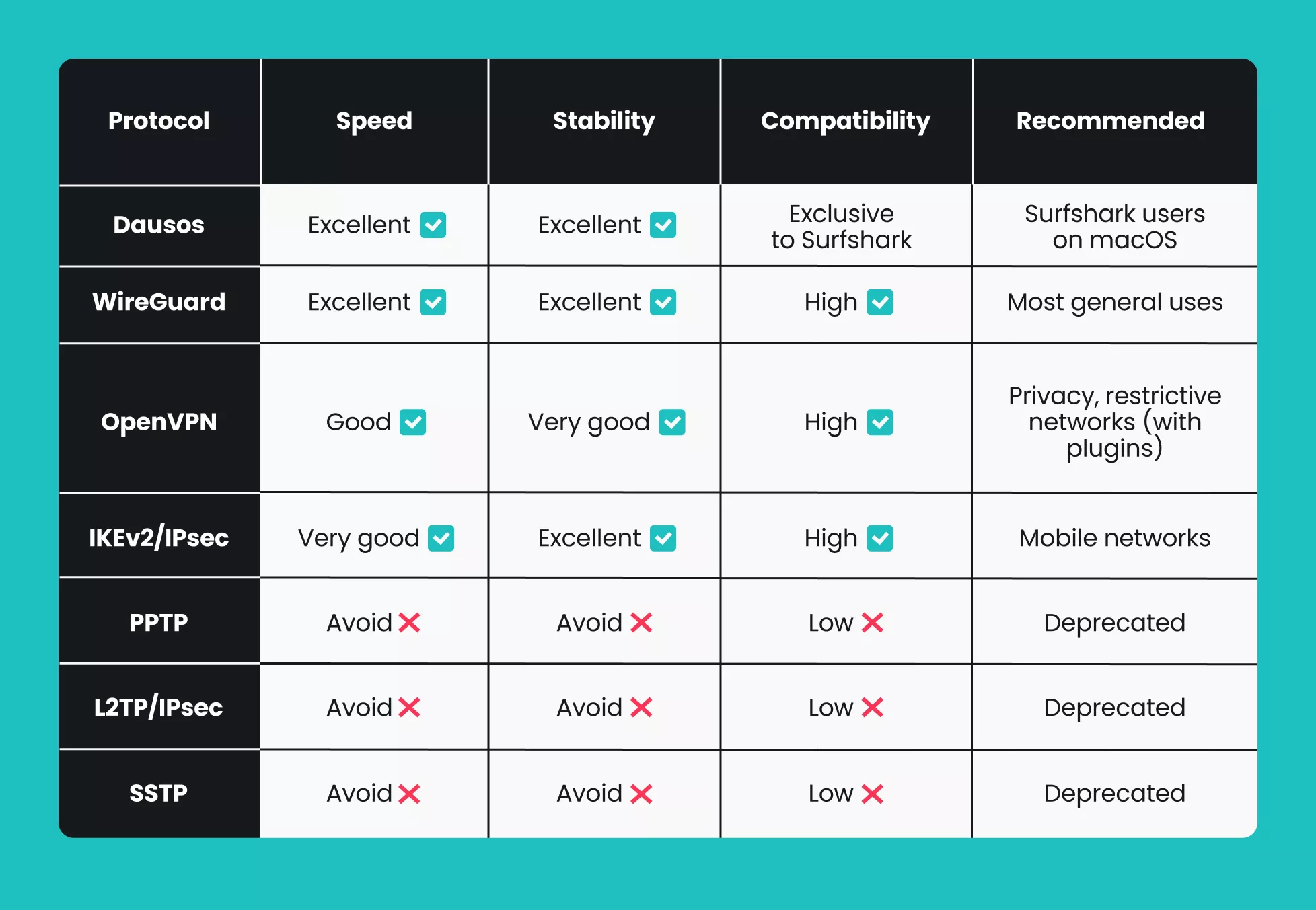
VPN protocol comparison
To help you choose a VPN encryption protocol that fits your needs best, we’ve compiled the above information on VPN protocols and their use cases, comparing them across key factors:
Conclusion: your choice of VPN protocol matters
Dausos offers the best combination of speed, stability, security, and ease of use for Surfshark users on macOS. For everyone else, WireGuard is a great choice.
In very specific and advanced cases, you might also find that OpenVPN and IKEv2/IPsec still have their place. However, remember that legacy protocols like PPTP, SSTP, and L2TP/IPsec are considered outdated and should generally be avoided.
FAQ
Which VPN protocol should I use?
Dausos is recommended for Surfshark users on macOS due to its superior performance, security, and speed. For other users, WireGuard is recommended, with OpenVPN and IKEv2/IPSec close behind.
What is the best type of VPN?
A remote access VPN is ideal for individuals seeking secure connections to private networks, while site-to-site VPNs are better for businesses linking multiple office locations. For personal use, a no-activity-logs VPN with strong encryption and a reputable provider is typically the best choice.
What is the latest VPN protocol?
The Dausos protocol from Surfshark is one of the latest VPN protocols, designed to be faster, more efficient, and more secure, with a consumer-first approach. WireGuard is another modern option that typically outperforms older protocols like OpenVPN and IPSec.
Is UDP a good choice for a VPN?
Yes, UDP offers faster speeds suitable for streaming or gaming. TCP is slightly slower but more reliable, particularly on restrictive networks.
What are the three most common VPN protocols?
The three most common VPN protocols are OpenVPN, IKEv2/IPSec, and WireGuard. While each has subtle strengths, WireGuard is generally considered the best of the three.



