Shield your personal data and stay private online with Surfshark’s industry-leading VPN encryption.
What is VPN encryption?
VPN (Virtual Private Network) encryption is a process that enciphers and secures data transmitted between your device and a VPN server.
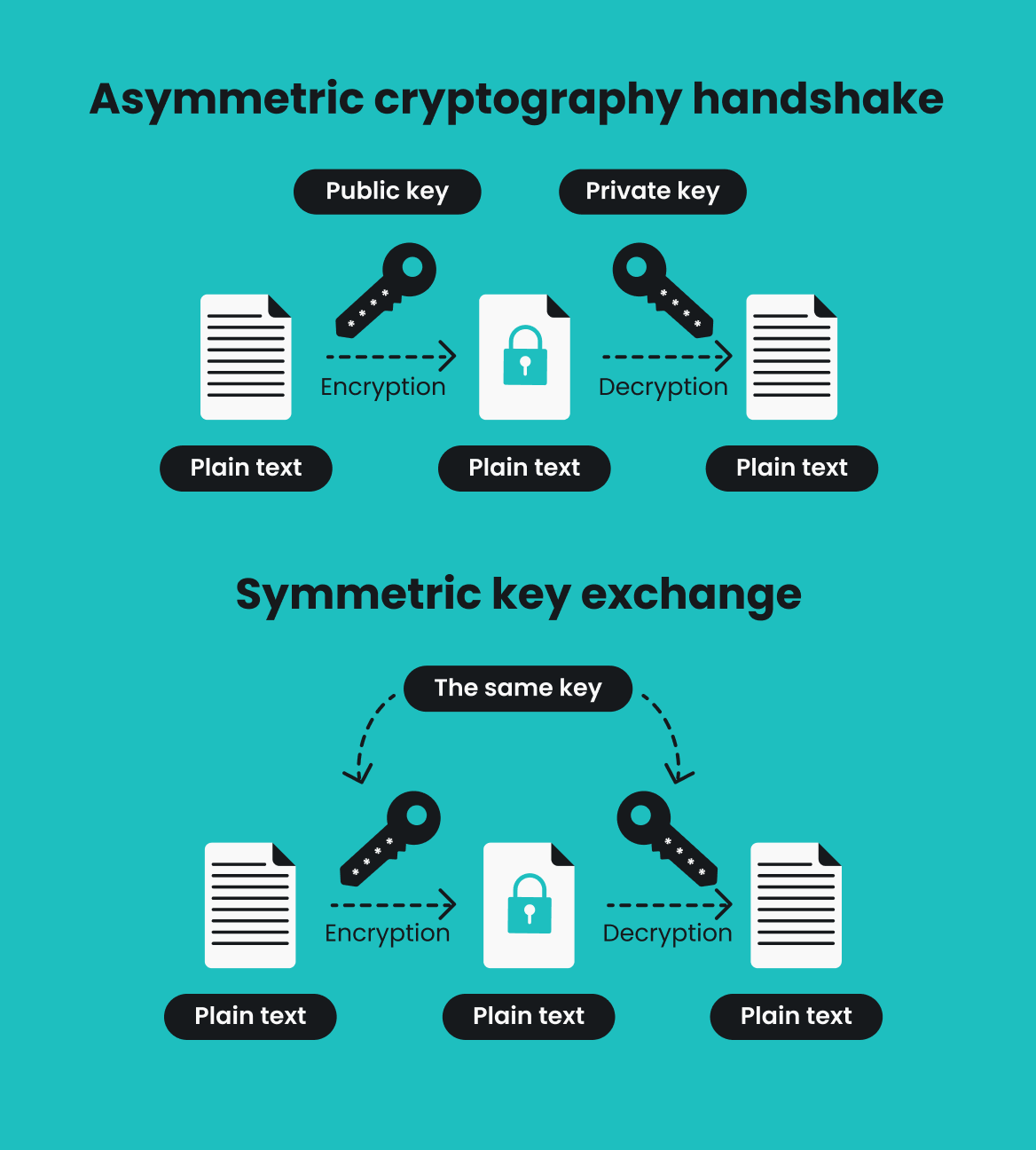
When you connect to a VPN, an encryption key is generated to encode and decode your data. Only you have the key, so even if a third party tries to intercept your connection, your encrypted data is scrambled and undecipherable.
Strong encryption is crucial to any VPN. That’s why trustworthy VPN service providers, including Surfshark, use AEGIS-256X2, AES-256, and ChaCha20 — some of the most effective encryption algorithms to date. AEGIS-256X2 encryption is used for the Dausos protocol, AES-256 for OpenVPN and IKEv2, and ChaCha20 for Wireguard.